Published September 19, 2017
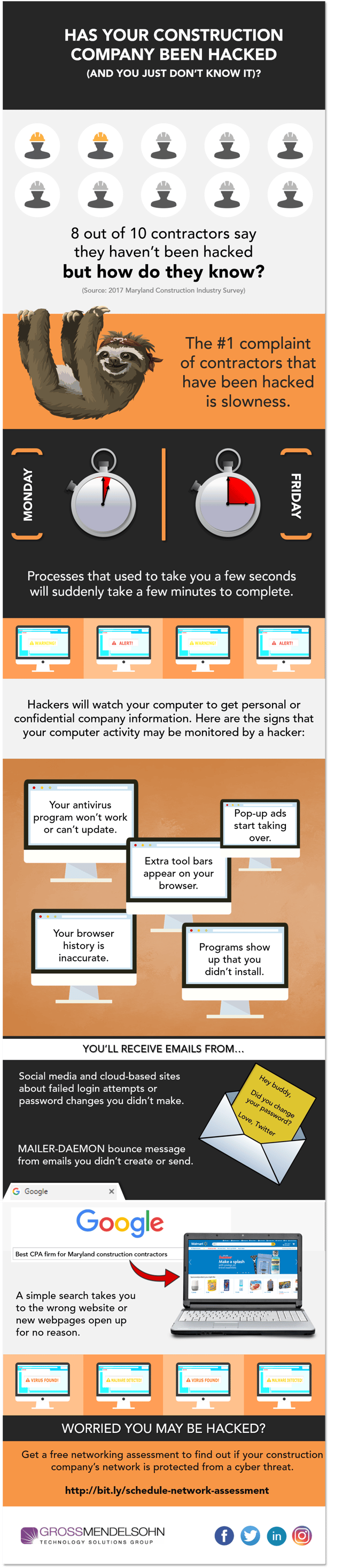
The #1 Sign — And Others — That Your Construction Company Has Been Hacked [Infographic]

By: Bill Walter
Cyber Security Wake-Up Call: What’s Putting Your Organization at Risk?
Learn how to lessen your exposure to cyber threats in this free webinar recording.

You May Also Be Interested In
The Top Technology Concern For Construction Contractors (And How To Solve It)
Contractors are constantly juggling multiple software solutions just to get through daily processes. When it comes to...
The #1 Sign — And Others — That Your Construction Company Has Been Hacked [Infographic]
Many construction contractors believe that being hacked means they’ll get a mysterious call from a person with a...